A private Twitter network for crypto has become one of the most powerful and misunderstood assets in Web3 marketing. As Crypto Twitter becomes more competitive, more censored, and more algorithm driven, organic visibility is no longer something that most projects can rely on. Thousands of new tokens, protocols, NFT collections, and DAOs launch every month, all competing for the same limited attention. Without a controlled distribution channel, even the best project narrative gets buried. A private network solves this by giving crypto teams something they never get from public platforms or influencers control over reach, engagement, and message delivery inside the Crypto Twitter ecosystem.
Most crypto founders still believe that success on X comes from posting more or buying followers. In reality, visibility is created by coordinated interaction. The algorithm rewards velocity, consistency, and social proof. A single tweet from a project account is almost invisible unless it is surrounded by replies, likes, retweets, and discussion from relevant crypto profiles. A private Twitter network is how professional teams manufacture that environment in a way that looks organic, feels real, and actually attracts genuine users.
This guide is designed to explain exactly how that system works. This article does not describe gimmicks, cheap bots, or unsafe automation. It shows how real crypto growth operations build, manage, and protect private Twitter networks that can support token launches, NFT mints, DeFi protocols, and long term brand building. By the end, you will understand what a private network really is, why most do it yourself attempts fail, and how professional platforms like CryptoGrowSocial and XLaunchPad provide a safer and more effective path to scalable Crypto Twitter growth.
Why Public Bot Tools Fail for Crypto Marketing?
Public bot tools are one of the biggest traps in Crypto Twitter marketing. They promise fast engagement, cheap followers, and automated growth, but they are built on infrastructure that was never designed for serious crypto campaigns. These platforms use shared servers, shared IP pools, and shared automation logic across thousands of users. That creates massive footprints that the X detection systems can see with ease. When one user abuses the system, every other account on the same network becomes more suspicious by association.
Another problem is engagement quality. Public tools generate generic likes, meaningless retweets, and random replies that do not align with crypto narratives. Crypto Twitter is not a general interest platform. It is a niche ecosystem where people follow specific chains, narratives, tokens, and influencers. When a project uses low quality engagement from irrelevant or obviously fake accounts, it sends a negative signal both to the algorithm and to real users. Instead of building trust, it destroys credibility.
There is also a serious control problem. With public bot tools, you do not own the accounts, the infrastructure, or the targeting. You are renting access to a pool of disposable profiles that can disappear at any moment. When bans happen, you have no recovery path. When a campaign needs to shift narrative or timing, you cannot adapt quickly. Professional crypto marketing requires precision and consistency, not random bursts of automated noise.
A few warning signs that show a tool is not suitable for crypto networks include:
- Accounts have no crypto related history or followers
- Engagement comes from the same visible set of profiles
- IP addresses are shared across hundreds of users
- There is no way to isolate or segment campaigns
- You cannot control how often or when engagement happens
This is why serious Web3 teams quickly abandon public bots and move toward private networks that give them full control over how engagement is created and delivered.
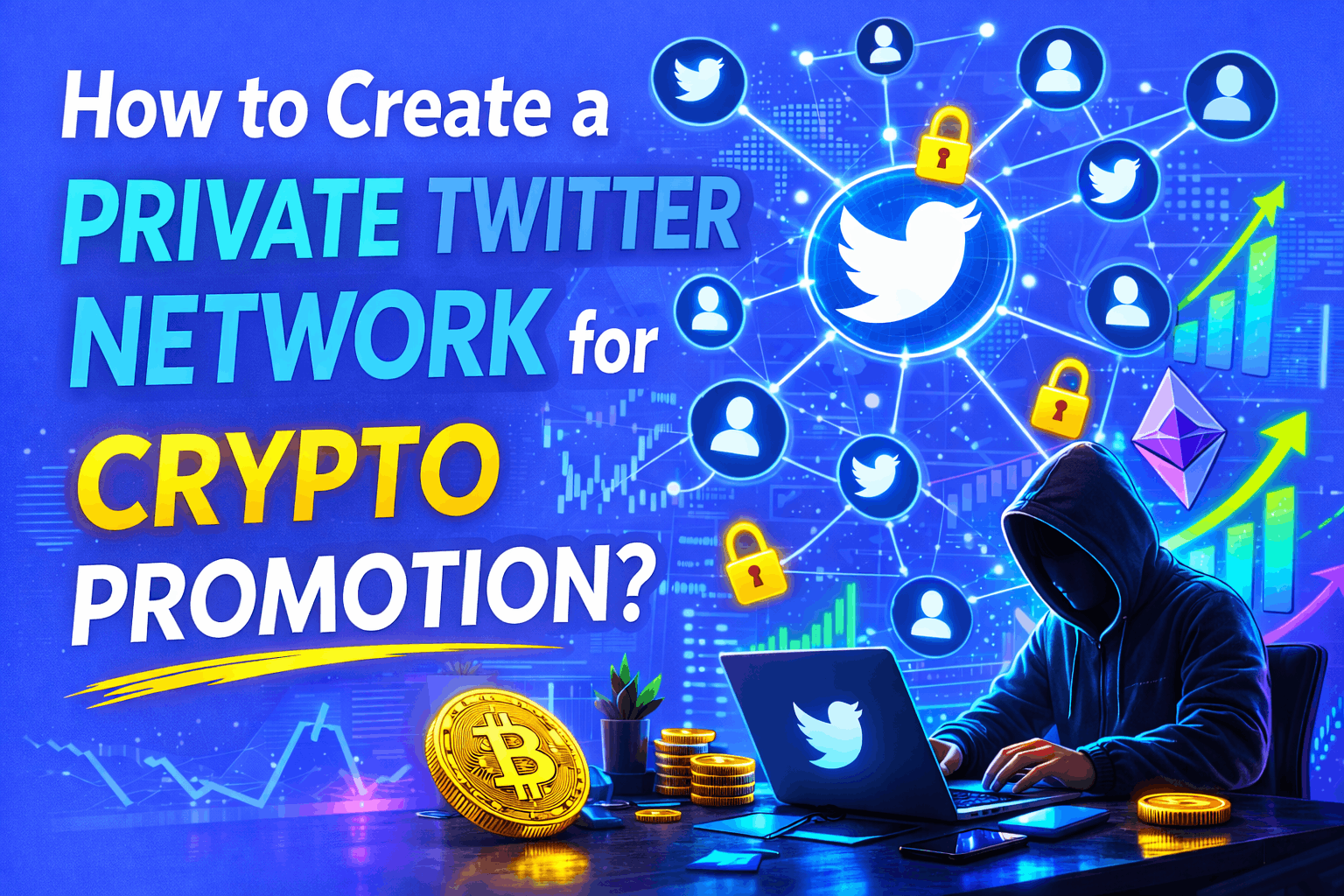
What a Private Twitter Network Really Is?
A private Twitter network is not just a group of accounts running on autopilot. It is an integrated system that combines identity, infrastructure, behavior, and targeting into a controlled growth engine. Each account in the network has its own personality, history, posting style, and crypto relevance. Each account runs on its own technical footprint, making it look like a real independent user. Together, these accounts form a coordinated community that can amplify any message inside Crypto Twitter.
The key difference between a private network and a bot farm is intentionality. A private network is built around narratives. Some accounts act as thought leaders, others as retail traders, others as community members. Some focus on retweeting, others on replying, others on starting discussions. When a project publishes a tweet, the network reacts in a way that looks like genuine community interest. That reaction increases reach, triggers the algorithm, and pulls in real users who see the activity and join the conversation.
Another defining feature of private networks is isolation. Each account operates on its own proxy, device profile, and session history. This prevents X from linking them together. Even if one account gets flagged, it does not put the rest of the network at risk. This kind of architecture is impossible to achieve with off the shelf tools.
A real private network includes:
- Accounts with crypto relevant bios, followers, and posting history
- Infrastructure that separates every account at the IP and device level
- Automation that respects human like timing and interaction patterns
- Targeting that focuses on crypto users rather than random audiences
- Monitoring that detects problems before bans happen
When all of these layers work together, a private Twitter network becomes one of the most powerful assets a crypto project can own.
Core Components of a Crypto Private Network
Every successful private Twitter network is built from four core layers that work together to create safe, scalable, and believable engagement. These layers are accounts, infrastructure, automation, and targeting. Weakness in any one of them can collapse the entire system.
The account layer is the foundation. Crypto networks do not use empty profiles. They use aged accounts that already have crypto related activity, followers, and engagement history. These accounts look like they belong in Crypto Twitter. They have followed the right people, talked about the right topics, and built credibility over time.
The infrastructure layer is what keeps those accounts alive. Each account needs its own proxy, device fingerprint, and login environment. This prevents linking. Without isolation, even the best accounts get burned. Professional networks invest heavily in private proxy pools, rotating device identities, and session persistence systems that mimic how real users behave online.
The automation layer is what allows the network to scale. Humans cannot manually control hundreds of accounts with the precision needed for modern crypto launches. Automation handles scheduling, retweets, replies, and engagement pacing. However, it must be designed to look human. Random delays, variable behavior, and role based logic are critical.
The targeting layer determines who the network interacts with. Crypto networks do not waste engagement on random users. They focus on people who follow crypto influencers, hold NFTs, talk about DeFi, or participate in Web3 communities. This ensures that engagement attracts the right audience and creates real growth.
Together, these layers form a system that can support anything from a token launch to a long term community building campaign.
Account Layer Building Crypto Native Profiles
The account layer is where most DIY crypto networks fail. Creating hundreds of new Twitter accounts and running them through automation does not work anymore. X can detect new account patterns, incomplete profiles, and unnatural growth very quickly. Professional crypto networks rely on aged accounts that already have history inside the ecosystem.
Aged crypto accounts have posted about Bitcoin, Ethereum, NFTs, memecoins, or DeFi long before they are added to a network. They follow crypto influencers, engage with token launches, and have followers who are real users. This makes their engagement far more valuable and far less suspicious.
Account personas are also carefully designed. Some accounts look like traders, others like developers, others like NFT collectors. This diversity makes the network feel real. When a project tweet goes live, different personas react in different ways. Some retweet with excitement. Some ask questions. Some quote tweet with analysis. This layered response looks like genuine community interest rather than automated promotion.
Healthy account building includes:
- Complete profiles with bios, avatars, and pinned tweets
- Posting history that matches the persona
- Follower and following patterns that make sense
- Gradual engagement growth rather than sudden spikes
- Interaction with the wider crypto ecosystem
This level of preparation takes time and resources, which is why professional providers maintain pools of ready to use accounts that can be deployed instantly when a campaign starts.
Infrastructure Layer How to Stay Invisible
Infrastructure is the invisible shield that protects a private Twitter network. Even the best accounts will get burned if they share IP addresses, devices, or browser fingerprints. X tracks far more than just usernames and passwords. It tracks how and where every account connects to the platform.
Each account in a professional crypto network runs on a private proxy. These proxies are not cheap data center IPs. They are residential or mobile IPs that look like real users. They are also geographically distributed to match the account’s persona and posting times.
Device fingerprinting is just as important. Every browser and operating system has unique characteristics. Professional networks use tools that generate unique device profiles for each account. This includes screen size, fonts, time zones, and dozens of other signals that X uses to identify users.
Session persistence ensures that accounts behave consistently. Real users do not log in from a new device every hour. Professional systems maintain long lived sessions so each account looks stable and predictable.
A secure infrastructure includes:
- One proxy per account with no sharing
- Unique device fingerprints for every login
- Long lived sessions that persist across activity
- Geographic consistency between IP and persona
- Continuous monitoring for anomalies
This layer is expensive and technically complex, which is why most DIY networks fail when they try to cut corners.
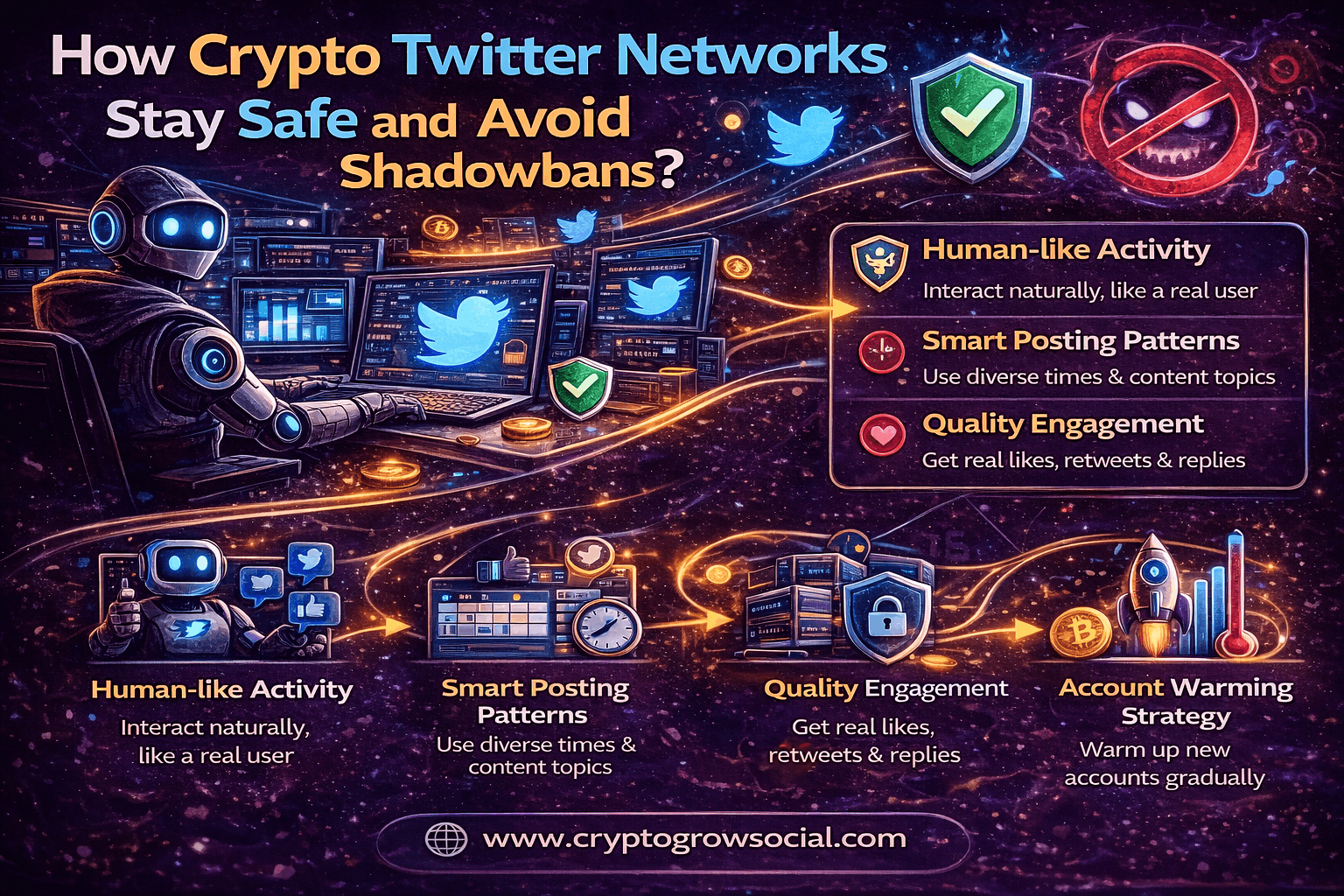
Automation Layer Safe Engagement at Scale
Automation is what turns a private network into a growth engine. Without automation, it would be impossible to coordinate dozens or hundreds of accounts across multiple campaigns. However, crypto automation must be built with safety and realism in mind.
Rate limits are critical. Each account can only perform a certain number of actions per day without looking suspicious. Professional systems carefully control how many likes, retweets, replies, and follows each account makes. These limits change over time as accounts age and build trust.
Randomization is another key factor. Humans do not act on exact schedules. Automation must include random delays, variable activity levels, and natural pauses. This prevents pattern detection.
Role based behavior adds realism. Not every account does everything. Some accounts mostly retweet. Some mostly reply. Some mostly post original content. This diversity makes the network look organic.
A safe automation framework includes:
- Daily and hourly action limits per account
- Randomized delays between actions
- Different behavior profiles for different personas
- Quiet periods where accounts do nothing
- Gradual scaling rather than instant full power
When automation is designed this way, it becomes almost impossible to distinguish from real user activity.
Campaign Layer Coordinated Crypto Promotion
The campaign layer is where strategy meets execution. A private Twitter network is not just a background noise machine. It is a narrative engine that supports specific moments in a crypto project’s life cycle.
Before a launch, the network can build awareness by engaging with related topics and influencers. During a token sale or NFT mint, it can create urgency and social proof. After a launch, it can sustain discussion, answer questions, and keep the project visible.
Campaigns are structured around phases. Each phase has its own tone, frequency, and type of engagement. Silence is just as important as activity. Too much engagement at the wrong time can look fake. Professional networks include cooldown periods and quiet windows to keep behavior realistic.
Elements of a strong campaign layer include:
- Pre launch warming and positioning
- Launch day amplification and support
- Post launch stabilization
- Ongoing community engagement
- Narrative alignment across all accounts
This is what separates a real growth system from random automation.
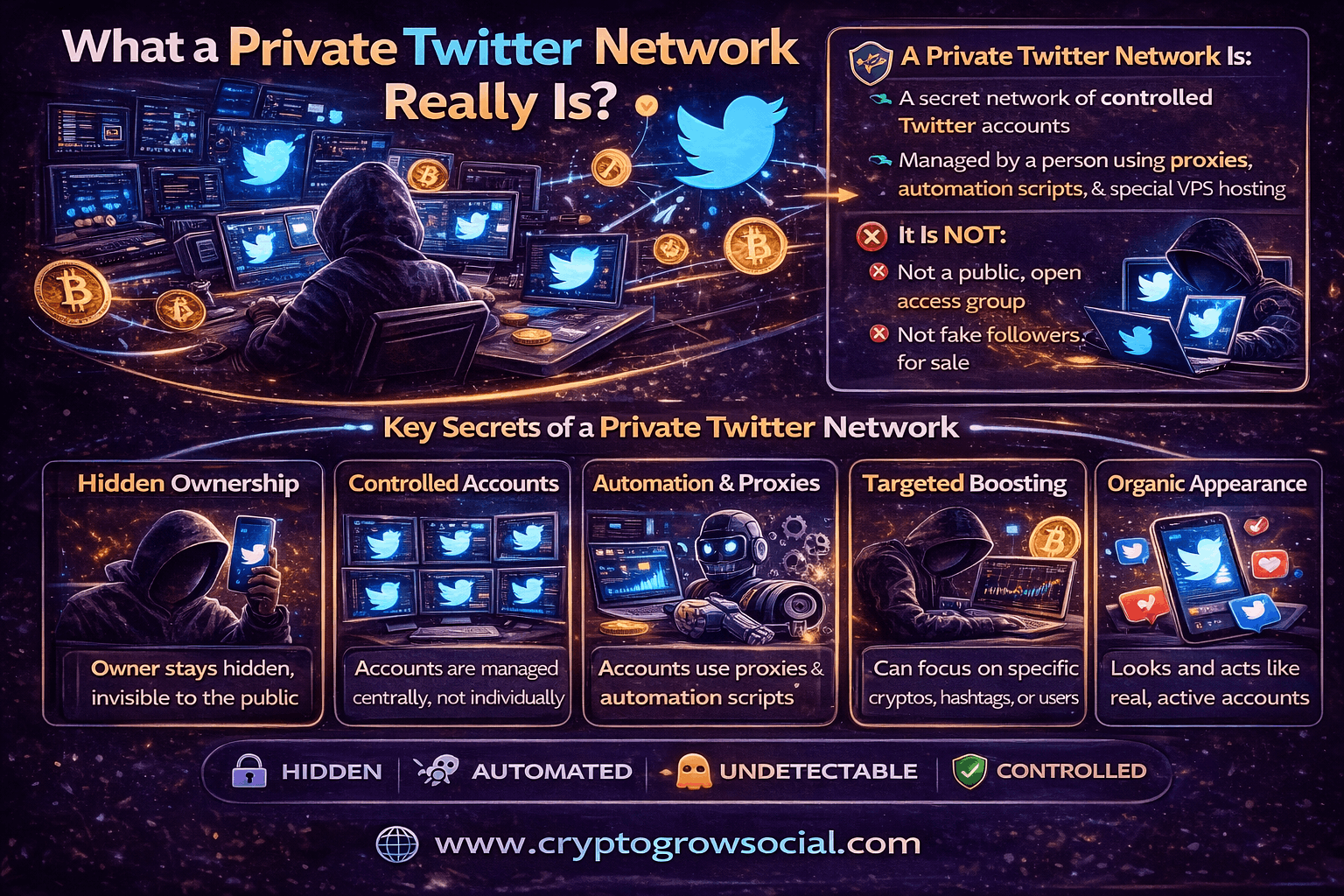
How Private Networks Avoid Bans and Shadowbans?
Avoiding bans is not about luck. It is about detection, reaction, and recovery. Professional private networks constantly monitor account health. They track reach, impressions, and engagement quality. Sudden drops in visibility can indicate a shadowban. Login challenges or captcha requests can signal increased scrutiny.
When a problem is detected, the system reacts. The affected account may be paused, cooled down, or rotated out. In some cases, its proxy or device profile is replaced. This prevents one small issue from spreading to the rest of the network.
Visibility checks are also important. Accounts regularly post test tweets and measure how they perform. If engagement drops across the board, it may indicate a larger infrastructure issue that needs to be fixed.
A safety focused network includes:
- Real time health monitoring
- Automatic cooldowns when risk increases
- Proxy and device rotation
- Account replacement pools
- Continuous performance tracking
This is how large crypto networks survive long term without being wiped out.
Why DIY Private Networks Fail?
Most do it yourself crypto networks collapse under their own weight. The first problem is footprint explosion. When dozens of accounts share the same IPs, devices, or automation patterns, detection becomes inevitable. The second problem is account quality. New or low quality accounts do not survive long enough to be useful.
The third issue is lack of monitoring. DIY setups rarely include systems to detect shadowbans or rising risk. By the time something goes wrong, it is too late to save the network.
Finally, most teams underestimate the cost and complexity. Building and maintaining private proxies, device profiles, and account pools requires constant investment and expertise. For most crypto projects, this distracts from what really matters building the product and the community.
How CryptoGrowSocial Builds Private Twitter Networks?
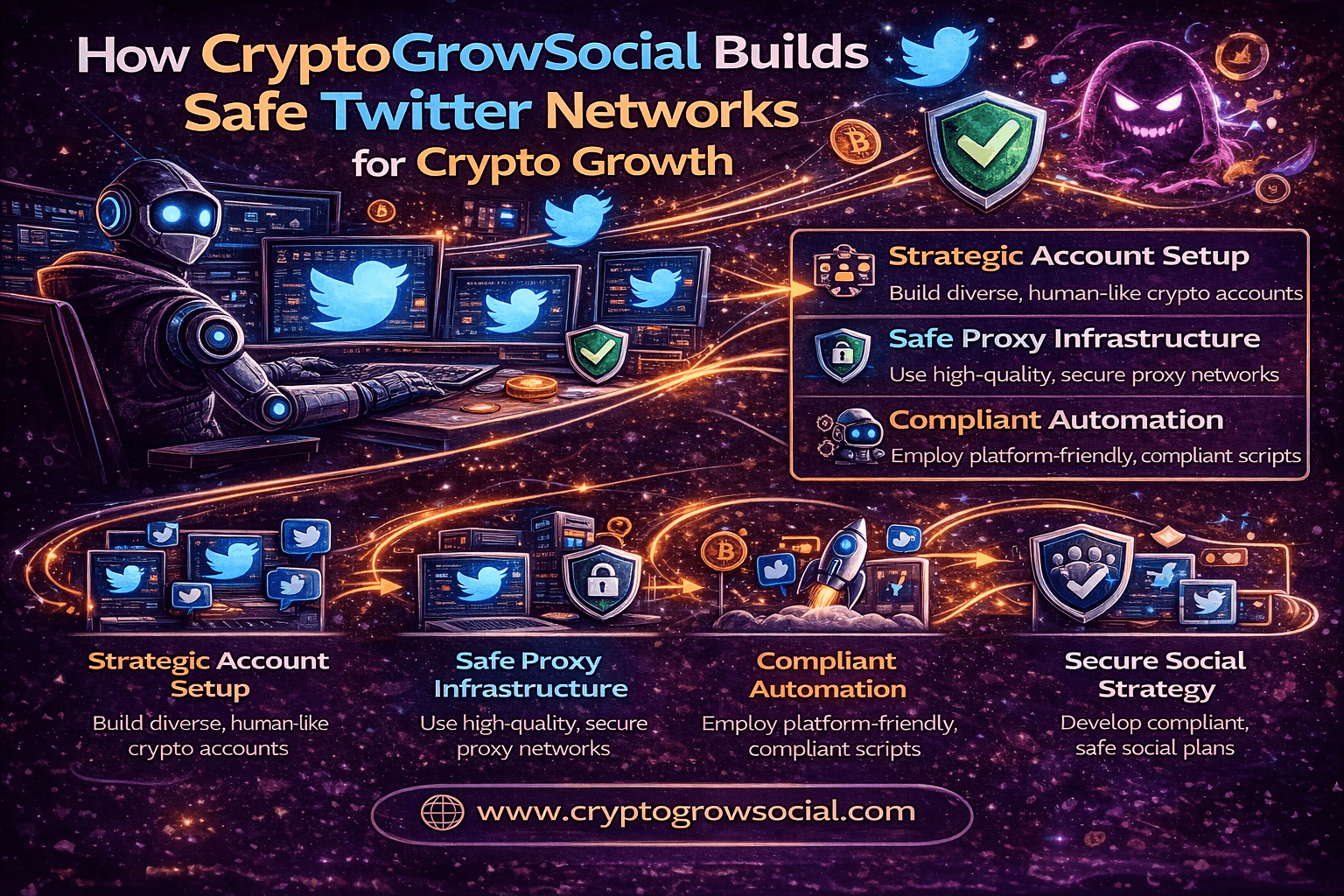
CryptoGrowSocial was created to solve one of the hardest problems in Web3 marketing: how to control distribution inside Crypto Twitter without risking bans, shadowbans, or reputation damage. Most teams either rely on organic reach that never scales or on cheap bot tools that destroy their accounts. CryptoGrowSocial was built to replace both with a professional private network ecosystem.
Unlike generic automation tools, CryptoGrowSocial does not sell software. It delivers a complete environment. This includes aged crypto native accounts, private infrastructure, safe automation layers, and crypto focused targeting. Every piece of the system is designed to work together.
The account layer is the foundation. CryptoGrowSocial uses profiles that already have posting history, followers, and activity inside the crypto space. These are not empty shells. They have interacted with real users, followed real projects, and participated in real conversations. This history makes their engagement believable and powerful.
The infrastructure layer is what keeps everything safe. Each account runs on its own private proxy and device profile. This prevents platforms from linking them together. Even if one account is flagged, the rest of the network remains invisible. This isolation is what separates professional networks from DIY setups that collapse overnight.
The automation layer controls behavior. CryptoGrowSocial does not run unlimited bots. Every action is paced, varied, and modeled after real human usage. Posting, retweeting, replying, and following are distributed over time so the network looks like a real community rather than a machine.
Finally, the targeting layer ensures relevance. Engagement is not random. Accounts interact with crypto users, crypto hashtags, and crypto conversations that match your project. This means every impression has a chance to become a real follower, a Discord join, or a token holder.
All of this is continuously monitored. Performance, engagement quality, and risk signals are tracked. Accounts are adjusted, rotated, or removed before they become liabilities. This turns Twitter automation from a gamble into a controlled growth system.
XLaunchPad vs XLaunchPad Pro for Private Networks
CryptoGrowSocial offers two ways to access its private network ecosystem. Both use the same professional grade infrastructure, but they are designed for different types of teams.
XLaunchPad is the fully managed option. This is built for founders, startups, and Web3 teams that want results without dealing with complexity. CryptoGrowSocial handles everything. Accounts are selected and assigned. Infrastructure is configured. Campaigns are executed. Engagement is managed. You simply provide your messaging, launches, and goals.
This model works best when you want to focus on building your product, your token, or your community while professionals handle distribution. You get the power of a private Twitter network without hiring growth engineers or learning how to run farms.
XLaunchPad Pro is designed for teams that want control. Agencies, marketing teams, and experienced growth operators get access to the same aged accounts, private proxies, and safe automation layers. The difference is that you design and run your own campaigns. You control schedules, intensity, narratives, and segmentation.
This gives you flexibility without forcing you to build infrastructure from scratch. You are not exposed to proxy problems, account sourcing, or detection risks. You get a clean, safe, professional environment to operate in.
Both options are built on the same foundation. Aged crypto accounts. Private infrastructure. Human like automation. Crypto focused targeting. The only difference is how much of the execution you want to handle yourself.
How to Launch Your Private Network with CryptoGrowSocial?
Launching a private Twitter network with CryptoGrowSocial is not a technical process. It is a strategic one.
Everything starts with your goals. Are you preparing for a token launch. An NFT mint. A protocol rollout. Or long term brand building. Each goal requires a different engagement profile. Hype looks different from education. Awareness looks different from conversion.
Based on this, CryptoGrowSocial assigns the right mix of accounts and personas. Some profiles are built to be loud. Some are designed to be credible. Some are positioned as traders. Others as builders or community members. This creates a network that feels real rather than artificial.
Next, campaigns are configured. Posting schedules are created. Engagement rules are defined. Target audiences are selected. The network is warmed up so activity looks natural before any major promotion starts. This is one of the most important steps because sudden spikes are what get accounts flagged.
Once live, the system runs continuously. Posts go out. Retweets and replies support them. Conversations form. Users start seeing your project again and again from different voices. Meanwhile, monitoring systems watch for risk, performance, and anomalies. If something looks wrong, it is adjusted before it becomes a problem.
From your side, you see results. More impressions. More followers. More conversation. More recognition. But you never have to touch a proxy, a bot, or a farm.
Why a Professional Private Network Is the Smartest Crypto Marketing Investment?
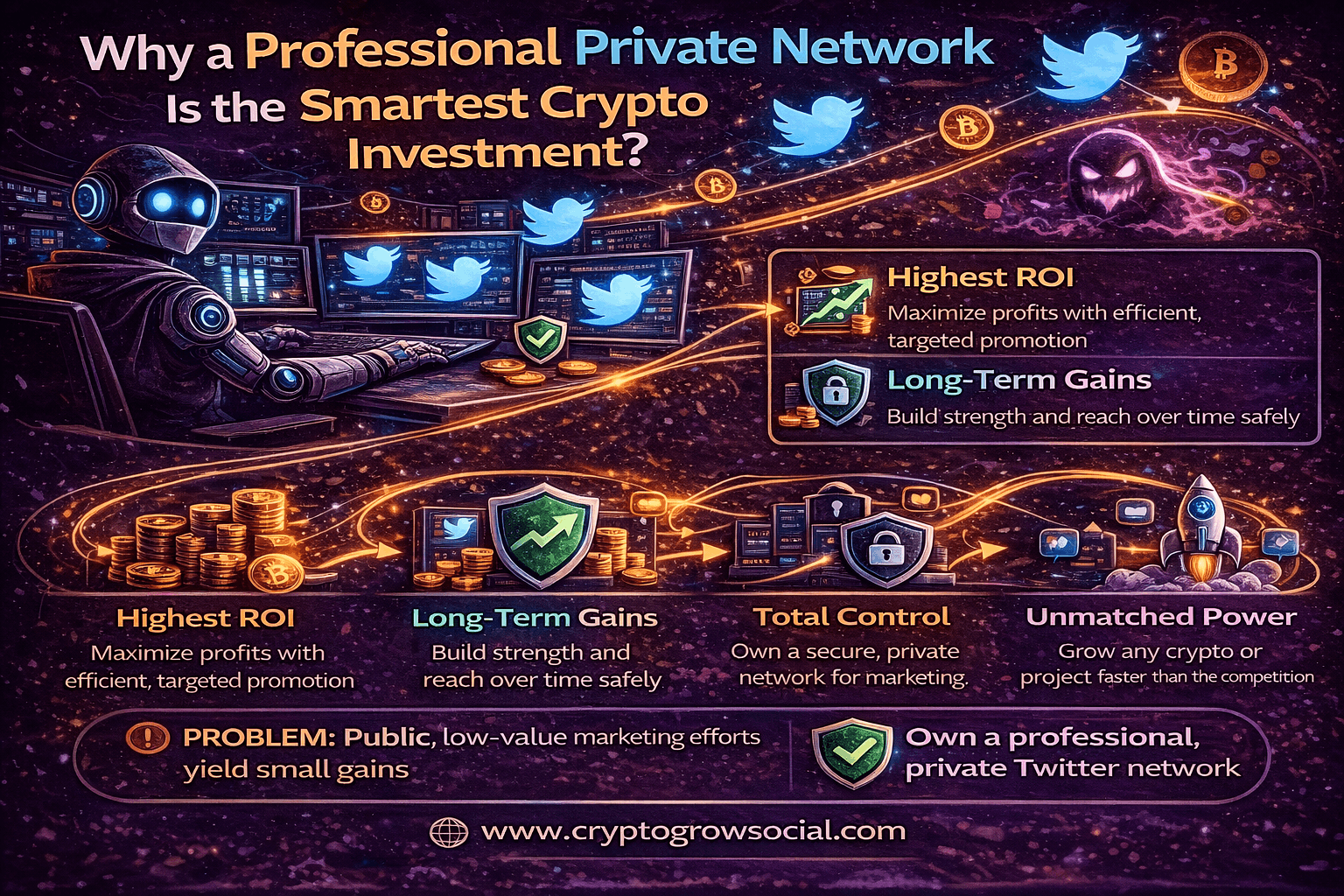
Crypto Twitter is not a fair market. It rewards visibility, not merit. The best technology in the world means nothing if no one sees it. A private Twitter network gives you the ability to create that visibility on demand.
Instead of hoping the algorithm notices you, you build a system that feeds the algorithm what it wants. Engagement. Activity. Relevance. Momentum. Every announcement you make is supported by a community that looks real because it is built from real looking accounts.
With a professional system, you are not just buying likes or followers. You are building a distribution channel that belongs to you. One that can be used for launches, partnerships, AMAs, listings, and every narrative you need to push.
This is what CryptoGrowSocial provides. Not bots. Not tools. But a private Crypto Twitter network that becomes a core asset of your Web3 business.
Conclusion
Building a private Twitter network for crypto promotion is no longer optional for serious Web3 teams. It is the foundation of modern Crypto Twitter growth. Trying to build one yourself is expensive, risky, and time consuming. Using public bot tools is even worse.
CryptoGrowSocial, through XLaunchPad and XLaunchPad Pro, gives you access to a professional grade private network that is safe, scalable, and designed specifically for crypto. Whether you want a fully managed solution or full control over your campaigns, the infrastructure is already built and tested.
If you are ready to stop guessing and start controlling your Crypto Twitter growth, CryptoGrowSocial provides the system that makes it possible.