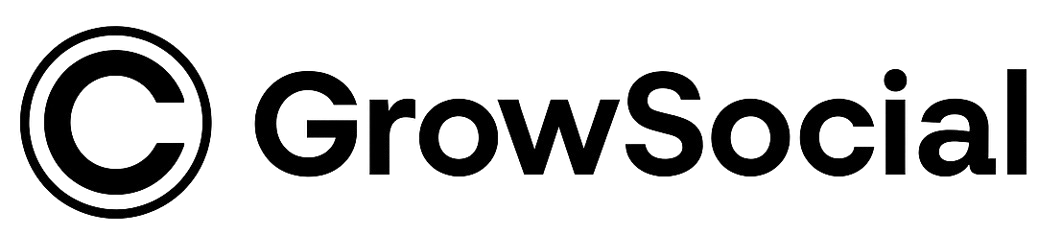
Security measures for protecting large Crypto Twitter networks are no longer optional. As crypto projects scale their marketing, they inevitably manage dozens, sometimes hundreds, of Twitter accounts working together to amplify content, build narratives, and create momentum. Each of these accounts becomes both an asset and a potential risk. One weak account, one misconfigured proxy, or one reckless automation rule can expose the entire network to detection, shadowbans, or permanent suspension. In a market where visibility is currency, losing a network means losing the ability to compete.
This article exists to explain what real security looks like for Crypto Twitter operations that run at scale. This guide walks through account level protection, infrastructure design, behavioral control, and monitoring systems that keep networks alive and profitable. If you are running or planning to run multiple crypto accounts for growth, understanding these layers of security is the difference between sustainable campaigns and catastrophic collapse.
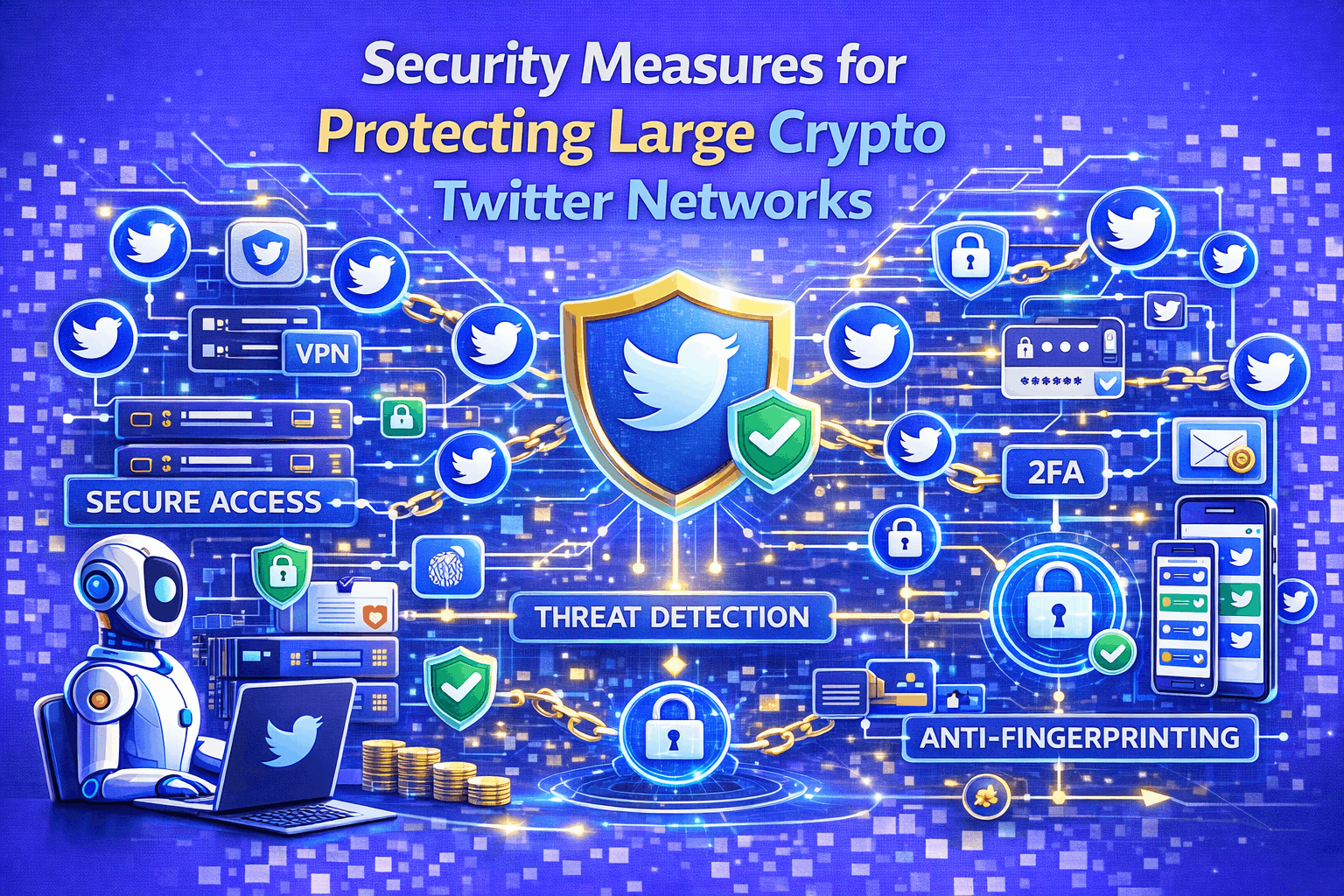
Why Crypto Twitter Networks Are High Risk Targets?
Crypto Twitter networks operate in one of the most aggressively monitored environments on social media. Platforms are constantly hunting for coordinated activity, artificial engagement, and manipulation. When a single crypto project controls dozens or hundreds of accounts that act together, it becomes an obvious target for automated detection systems.
Crypto networks attract extra scrutiny for several reasons. They move fast. They create spikes in engagement. They focus on financial topics. They generate hype around tokens, launches, and price action. All of this makes their behavior look very different from normal social media users.
A large Crypto Twitter network usually performs actions such as retweeting, replying, liking, and following in coordinated patterns. If these patterns are not carefully controlled, they create fingerprints that detection systems can identify. These fingerprints include shared IP addresses, similar device profiles, identical posting schedules, and repetitive behavior across accounts.
Even one mistake can create a chain reaction. When one account is flagged, platforms often analyze its interactions. If they find that it frequently engages with the same group of accounts, those accounts also become suspicious. This is how entire networks disappear overnight.
Crypto projects also face attacks from competitors, trolls, and reporting campaigns. Large visible networks attract attention. Without strong security, a coordinated report can push an already fragile network over the edge.
This is why Crypto Twitter networks are inherently high risk. They are powerful, but only when protected by professional grade security at every layer.
Account Level Security Fundamentals
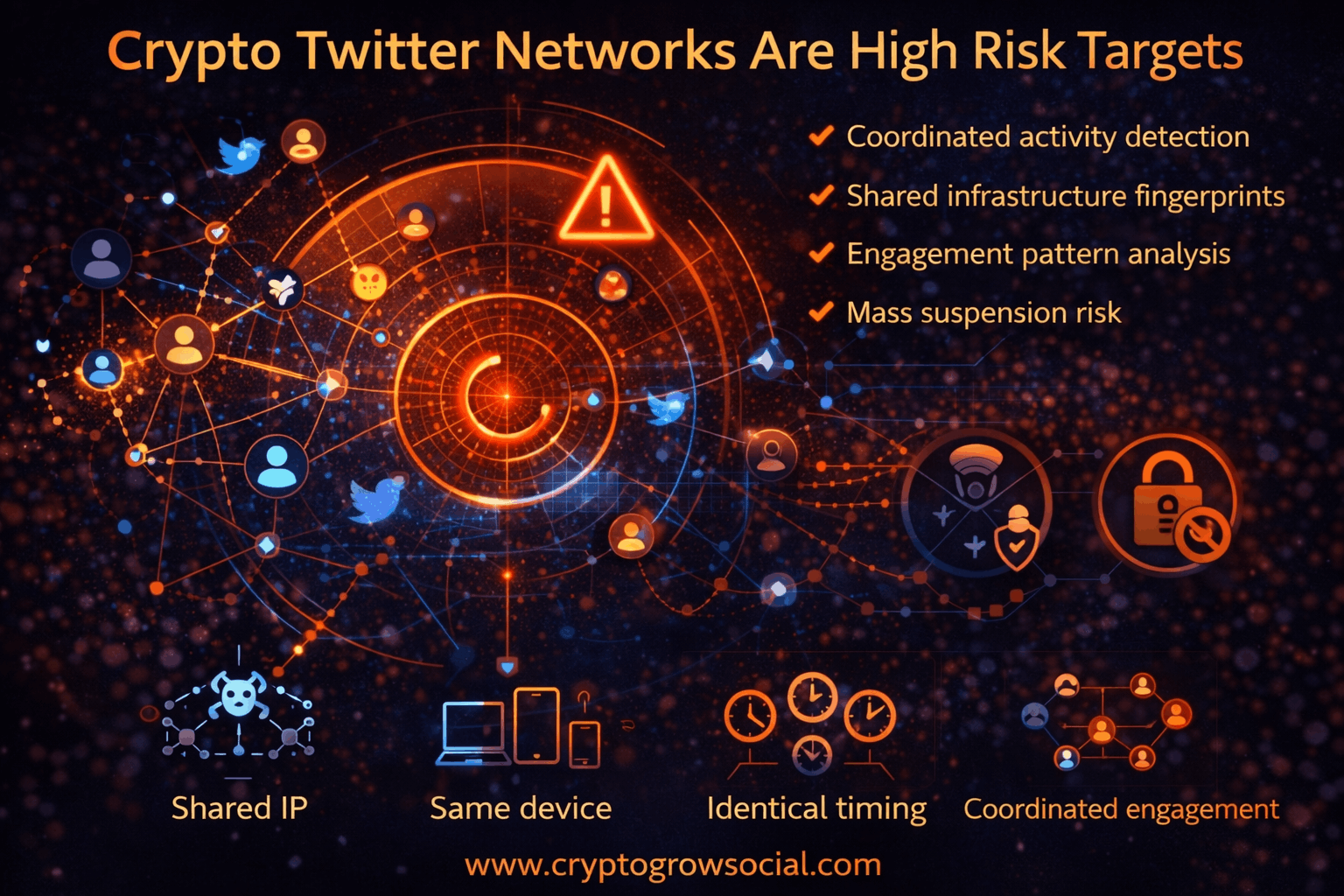
At the foundation of every secure Crypto Twitter network are the accounts themselves. Many people think account security is simply about passwords and two factor authentication. In reality, for large networks, account security is about credibility, history, and behavioral stability.
Aged accounts are the first requirement. Accounts that have been active for months or years, that have posted naturally, followed real people, and participated in crypto conversations carry trust signals. New accounts do not. When new accounts suddenly begin heavy engagement, they are far more likely to be flagged.
Each account should have:
- A unique and realistic profile
- A history of organic activity
- Followers and following that make sense
- A posting style that looks human
Credential security matters too. Using the same email provider, phone number source, or recovery method across many accounts creates links that platforms can see. A professional system uses diverse and isolated credentials for every account.
Two factor authentication should be enabled, but that is only the surface. What matters more is that accounts are not accessed from multiple environments or devices. If one account logs in from different countries or machines within short periods, it looks compromised.
Session stability is another overlooked factor. Logging out and back in too often, switching tools, or using multiple apps to control the same account creates unusual patterns.
A secure network treats every account like a real person. One identity, one environment, one behavioral history.
Infrastructure and Proxy Management
Infrastructure is where most Crypto Twitter networks fail. Cheap setups run dozens of accounts through the same server or a small pool of shared proxies. This creates IP clusters that detection systems can identify instantly.
Professional infrastructure isolates every account. Each one runs on its own private proxy, often residential or mobile, that looks like a real internet connection. These proxies are geo distributed, matching the profile of the account.
Beyond IP addresses, device fingerprints matter. Platforms track browser type, operating system, screen size, fonts, and dozens of other signals. When many accounts share the same fingerprint, they appear linked.
A secure infrastructure includes:
- One proxy per account
- One device profile per account
- Stable geographic locations
- Long term IP assignments
Switching proxies too often is just as dangerous as sharing them. A real user does not change internet providers every day. Stability builds trust.
Networks also need redundancy. If a proxy fails or is flagged, the account should be rotated to a new one carefully, without sudden jumps that look suspicious.
Infrastructure is not something that can be improvised. It must be designed to mimic thousands of independent users.
Behavioral Pattern Control
Even with perfect accounts and infrastructure, behavior can still expose a network. Platforms do not just look at where actions come from. They look at how they happen.
Human behavior is messy. People do not like, retweet, and reply at fixed intervals. They do not act twenty four hours a day. They have pauses, bursts, and randomness.
Automation systems must recreate this. Every account in a network should have:
- Different active hours
- Variable delays between actions
- A mix of engagement types
- Days with more activity and days with less
If one hundred accounts retweet the same post within thirty seconds, that is not organic. If they do so over hours, mixed with likes, replies, and other activity, it looks natural.
Content interaction should also be varied. Accounts should not only engage with one project. They should also interact with other crypto content, trends, and conversations.
This creates a web of believable behavior that hides the network inside the broader ecosystem.
Monitoring and Risk Mitigation
No system stays safe without monitoring. Crypto Twitter platforms constantly adjust their detection methods. What was safe last month may not be safe today.
A professional operation watches:
- Engagement success rates
- Sudden drops in reach
- Login challenges
- Account restrictions
- Shadowban indicators
When something changes, action is taken. Accounts can be slowed down, paused, or rotated. Campaigns can be adjusted. Infrastructure can be refreshed.
This prevents small issues from becoming network wide disasters.
Without monitoring, most networks only notice problems after accounts start disappearing.
How CryptoGrowSocial Secures Crypto Twitter Networks?
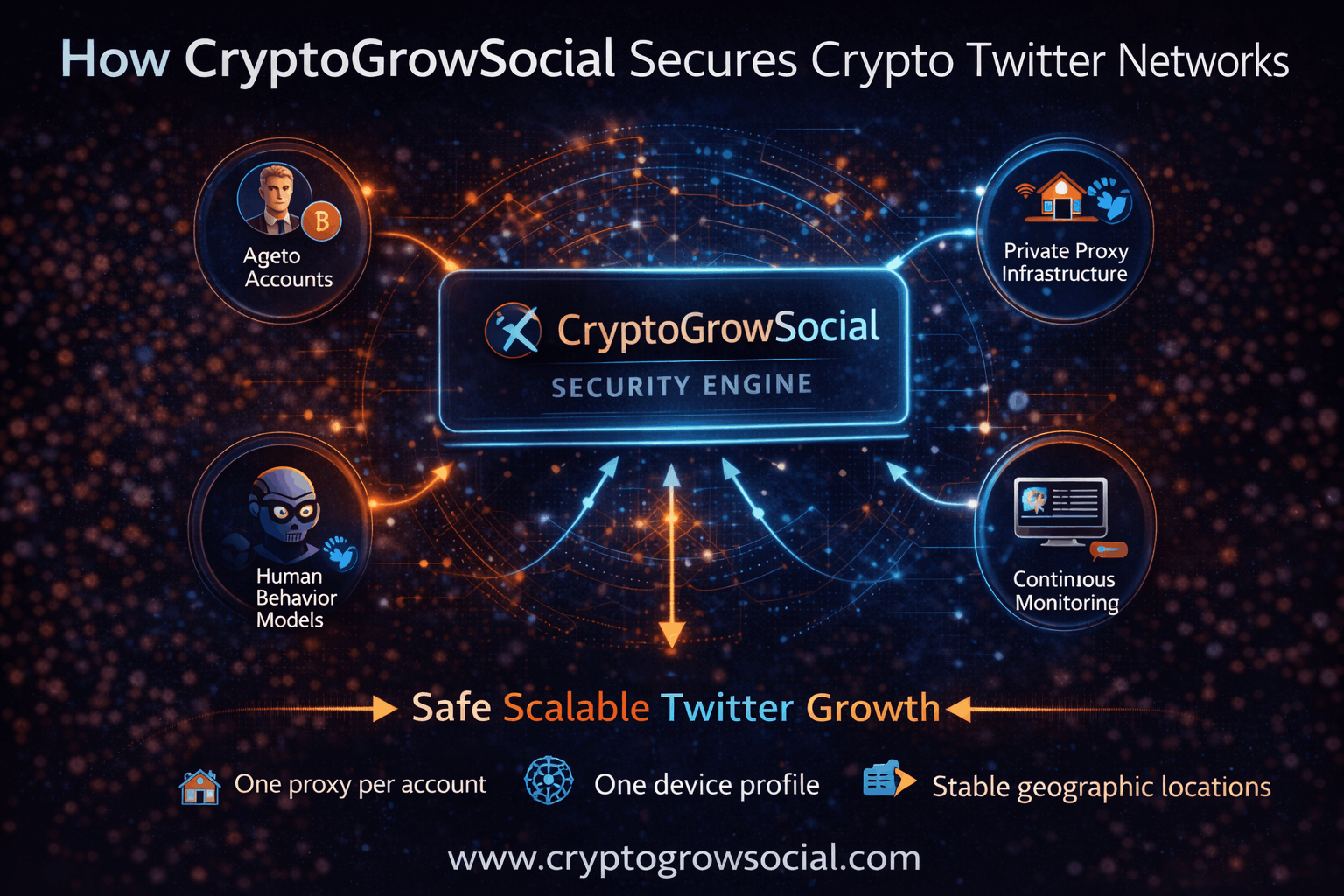
Securing a Crypto Twitter network is not a side concern. It is the backbone of any growth strategy that operates at scale. CryptoGrowSocial was built with this truth at its core: growth without security is fragile, short lived, and eventually self-defeating. While many tools automate actions, very few systems protect accounts, infrastructure and campaign logic in a way that keeps a network alive and effective over weeks and months of activity. CryptoGrowSocial is different because it does not treat security as an add-on. It treats security as the foundation upon which growth is built.
Through its flagship solutions XLaunchPad and XLaunchPad Pro, CryptoGrowSocial provides an integrated security architecture that allows crypto projects, marketing teams, launchpads and agencies to scale Twitter campaigns with confidence. This architecture mitigates detection risk, preserves account health and enables continuous engagement without exposing accounts to platform flags or bans. Below is how CryptoGrowSocial does it.
1. Aged Crypto Native Accounts with Built-In Credibility
One of the biggest vulnerabilities in DIY automation is the use of newly created or low quality accounts. These accounts have no history, no real engagement, and almost no context within the crypto ecosystem. Platforms like X can easily spot them because they behave differently from real users.
CryptoGrowSocial solves this by providing aged, crypto native accounts. These profiles have been cultivated over time with real activity, meaningful follower connections, and authentic engagement. They already participate in crypto conversations, follow relevant accounts, and have history that gives them legitimacy. When these accounts interact with your project content, it appears as genuine community interest rather than fake or spammy behavior.
This provides three major security benefits:
- Organic footprint – aged accounts look like real users rather than bot shells.
- Behavioral context – they have a posting history that aligns with crypto norms.
- Engagement trust – platforms are far less likely to flag them because they behave like real users.
Whether you use XLaunchPad or XLaunchPad Pro, these crypto native accounts become the engine that amplifies your messages without creating detectable patterns.
2. Private Proxy and Device Infrastructure for Isolation
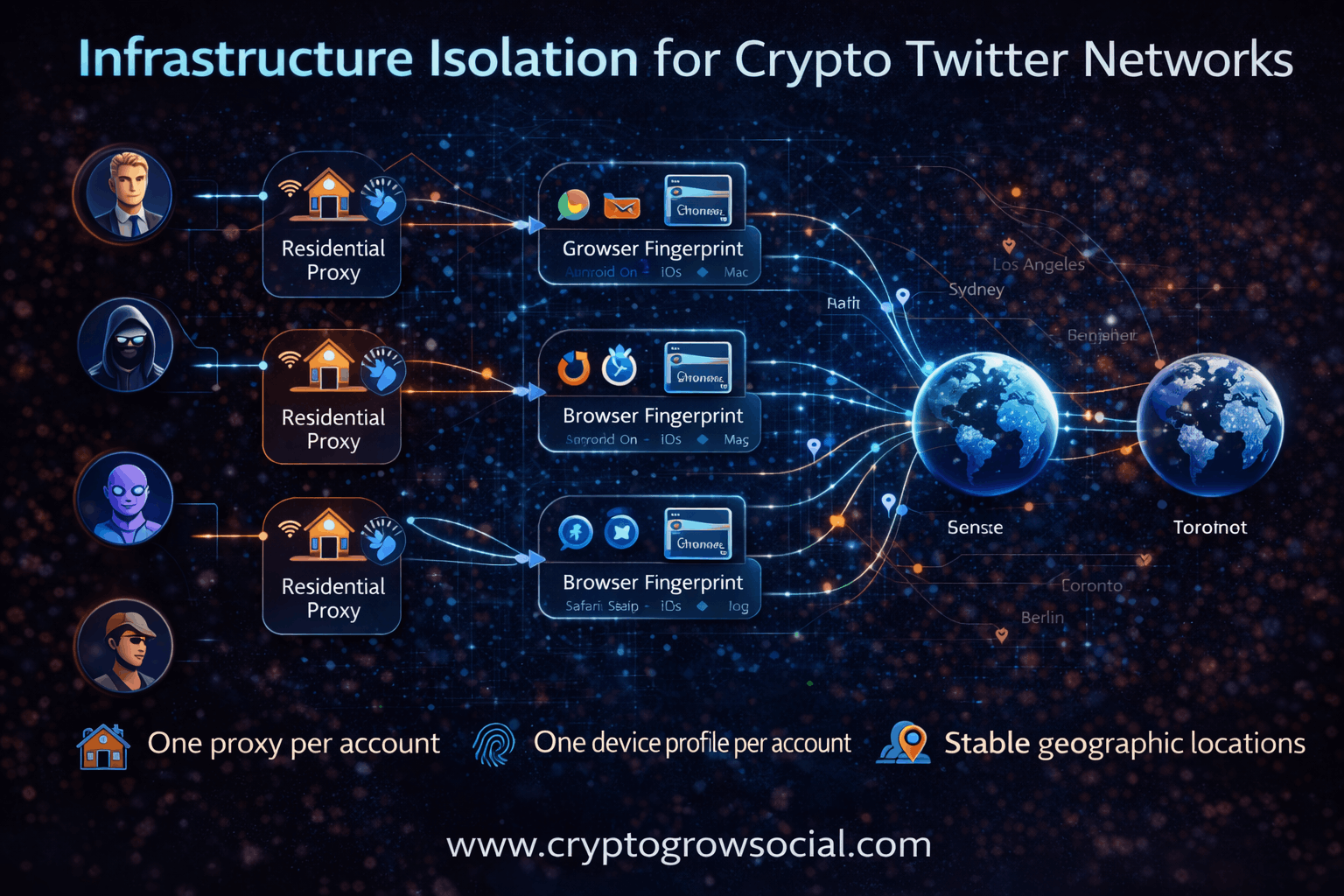
Accounts are only as safe as the environments from which they operate. Cheap automation services often run dozens of accounts behind the same IP ranges or shared proxy pools. This creates patterns that platform detection systems can flag quickly. When multiple accounts appear to come from the same digital footprint, the risk of network-wide penalties increases dramatically.
CryptoGrowSocial eliminates this risk by using private proxy and device infrastructure. Every account is assigned its own proxy and unique device fingerprint so that it behaves like a real human user on a dedicated device.
Here is what this infrastructure provides:
- One proxy per account – no shared IPs that link accounts together.
- Unique device fingerprints – each account mimics a distinct browser, operating system and device setup.
- Session persistence – accounts maintain consistent access, avoiding suspicious login patterns.
- Geographical diversity – proxies are distributed across locations consistent with real global usage.
This level of isolation ensures that actions from different accounts cannot be correlated by platform detection systems. Accounts operate as independent identities, which drastically reduces detection risk.
3. Behavior Models Tuned for Crypto Twitter Patterns
Security is not just about infrastructure. It is also about how accounts behave. Human users do not act with machine precision. They have timing variation, irregular patterns, contextual engagement and gaps in activity. Most automation tools ignore this reality and create predictable behavior patterns that detection systems learn to identify.
CryptoGrowSocial avoids this with behavior models tuned specifically for Crypto Twitter. These models generate engagement actions that mimic real human nuance. Instead of retweeting everything instantly, accounts spread actions over time. Instead of replying at flawless intervals, there are pauses, delays, and variations that look natural. Instead of following the same timing patterns across accounts, each one has its own rhythm.
These behavior models are important because they:
- Reduce artificial patterns that trigger detection systems
- Create realistic activity that blends into organic user traffic
- Allow accounts to interact contextually rather than mechanically
This is especially critical when managing multiple campaigns simultaneously, because predictable automation is one of the strongest signals platforms use to identify non-human behavior.
4. Campaign Based Engagement with Contextual Controls
Crypto projects do not grow by random activity. They grow when posts are supported by a network that understands narrative, timing, and audience relevance. Many automation systems apply the same actions to everything, leading to noise instead of influence.
CryptoGrowSocial uses campaign based engagement to ensure that every action supports a strategic goal. Whether you are running a presale, a listing announcement, a community event, or a meme push, each campaign can be configured with its own logic, timing and intensity.
This system provides:
- Phase based action rules – different behavior for launch, hype, post-launch
- Engagement prioritization – high priority posts get more attention
- Audience contextualization – engagement varies by segment
Because engagement is driven by campaign logic rather than blind automation, the system avoids not only detection but also wasted actions. Each interaction has a purpose, and this increases both safety and effectiveness.
5. Continuous Monitoring and Optimization
Security is not static. Platform detection systems evolve. What was safe yesterday might be unsafe today. Many DIY systems fail because they lack the ability to see when accounts are being limited, shadowbanned or losing reach. By the time teams notice, significant damage has already been done.
CryptoGrowSocial solves this with continuous monitoring and optimization. Every account’s health, engagement performance, reach and risk indicators are tracked in real time. When anomalies appear, the system can take action:
- Slow down activity
- Rotate accounts
- Adjust proxies
- Modify behavior patterns
- Pause risky campaigns
This proactive approach ensures that potential problems are caught before they snowball into catastrophic losses. It transitions automation from a reactive tool into a proactive growth engine.
Comparison: Guessing vs Tested System
Without a professional security system, teams often guess at how to keep accounts safe. They hope rate limits, random delays, or cheap proxies will be enough. What they overlook is that platform detection is probabilistic, adaptive, and increasingly sophisticated. Simple tricks that worked once are flagged quickly tomorrow.
CryptoGrowSocial has been tested across thousands of accounts and campaigns. Its security architecture is the result of observing how real detection systems behave and how real crypto audiences interact. Instead of guessing, your project benefits from accumulated experience embedded into a robust infrastructure.
This means crypto teams can stop worrying about security and focus on strategy:
- Messaging
- Launch planning
- Community management
- Partner relations
- Narrative control
CryptoGrowSocial protects the network so teams can execute their vision with confidence.
Summary of How CryptoGrowSocial Secures Your Network
To bring this together, CryptoGrowSocial provides:
Aged crypto native accounts that already have credibility and context
Private proxy and device infrastructure that isolates each identity
Behavior models tuned for human like activity in the crypto space
Campaign based engagement logic that supports strategic goals
Continuous monitoring and optimization that catches risks early
This ecosystem turns automation from a risky experiment into a sustainable growth engine that operates safely within platform expectations.
When scaling on Crypto Twitter, safety is not optional. It is the foundation of visibility, trust and long-term influence. With XLaunchPad and XLaunchPad Pro, CryptoGrowSocial provides a security first architecture so crypto projects can grow faster, safer and with real audience impact.
Conclusion and How to Run Secure Crypto Campaigns
Security measures for protecting large Crypto Twitter networks determine whether your marketing survives or dies. If you want to run serious crypto campaigns without constant fear of bans and losses, you need a professional system.
CryptoGrowSocial provides that foundation through XLaunchPad and XLaunchPad Pro. It gives you the security, scale, and stability needed to grow a real presence on Crypto Twitter.
If your project depends on visibility, protecting your network is not optional. It is where success begins.