Crypto Twitter and the wider X platform have evolved into one of the most competitive attention markets in the world, especially for Web3 projects, token launches, trading communities, and decentralized protocols that rely on fast-moving narrative momentum to survive. Every day, thousands of new crypto accounts attempt to gain traction, but only a small fraction ever reach meaningful visibility, not because their technology is weak, but because the algorithm never gives them a chance to be seen. This reality has created a new operational layer inside crypto marketing: multi-account engagement systems designed to amplify ideas, seed conversations, and accelerate distribution without triggering suppression.
However, running multiple Twitter accounts is no longer about creating bots and spamming content. X has invested heavily in behavioral analysis, device fingerprinting, and network detection systems that can suppress entire account clusters within hours if they behave in a way that looks artificial. For crypto teams, founders, growth hackers, and narrative operators, the challenge is no longer how to run many accounts, but how to make many accounts behave like independent humans who just happen to share similar ideas. That is what undetectable multi-account engagement actually means.
Why Multi-Account Strategies Fail for Most Teams?
Most crypto teams fail with multi-account strategies not because the idea is flawed, but because their execution misunderstands how modern social platforms detect manipulation. Many people still believe that Twitter bans accounts because they are “bots.” In reality, Twitter rarely cares whether something is automated or manual. What it cares about is statistical abnormality.
When a group of accounts begins behaving in ways that no organic group of humans would ever behave, the platform quietly restricts their reach, slows their impressions, and eventually suppresses them entirely. This is called shadowbanning, and it is far more dangerous than account deletion because most users never realize it has happened. Their posts still appear to be live, but nobody sees them.
Crypto teams are especially vulnerable because they tend to operate in tight clusters. Their accounts follow the same traders, reply to the same threads, push the same narratives, and often use similar language. Without proper separation and behavioral entropy, even well-funded projects end up building networks that Twitter identifies as coordinated manipulation instead of organic communities.
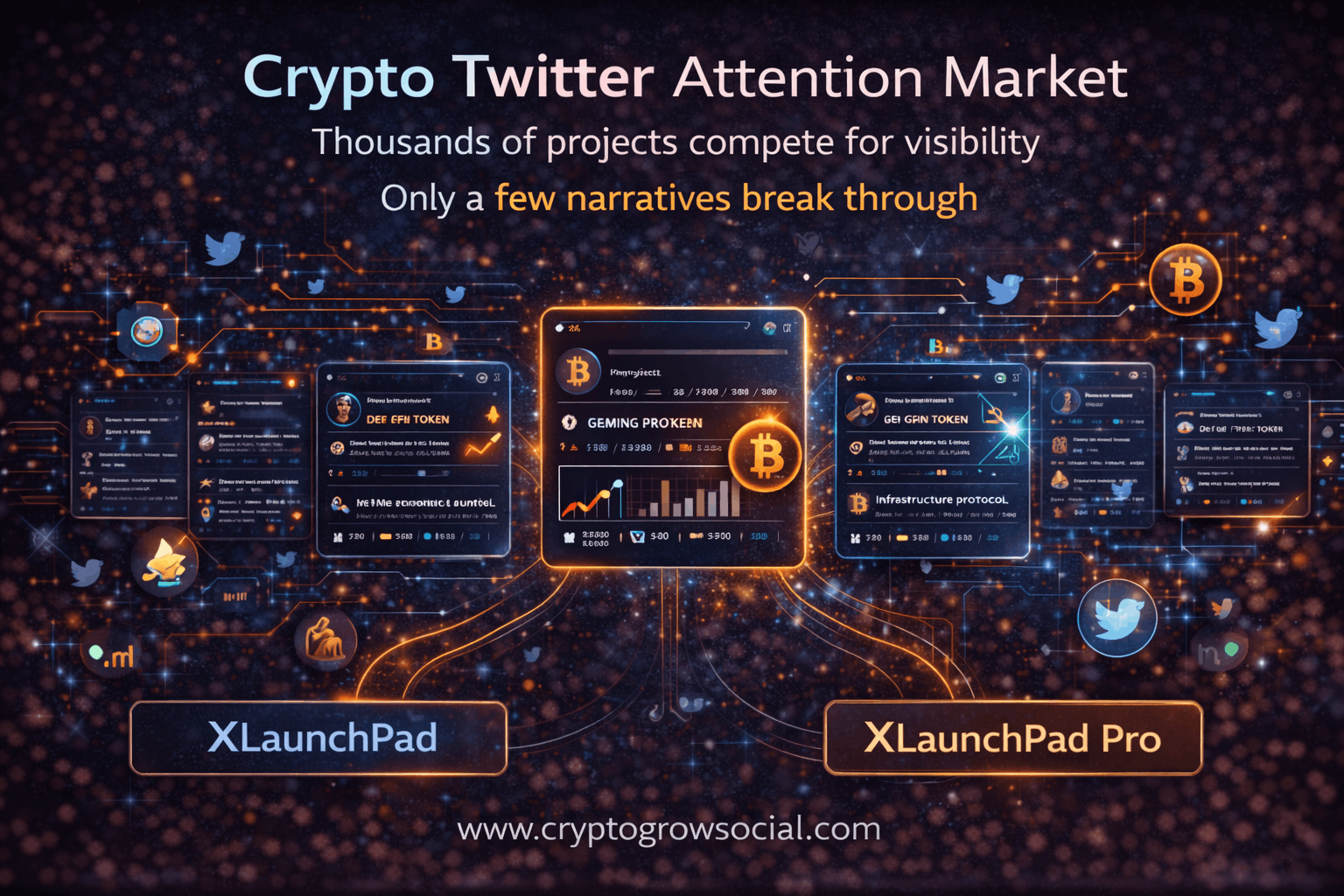
How Twitter (X) Detects Coordinated Accounts?
To understand how to avoid detection, you must first understand what Twitter is actually looking for. The platform does not need to read your content to detect a network. It reads metadata, patterns, and relationships.
Twitter’s internal systems are designed to identify clusters of accounts that move together too often, too similarly, and too predictably. These clusters are not defined by what they say, but by how they behave.
IP Correlation
Every time an account logs in, posts, likes, or replies, Twitter records the IP address and subnet. When many accounts repeatedly act from the same IP ranges, they begin to look like one operator. Data center proxies are particularly dangerous because hundreds of unrelated users may already be flagged inside those ranges. Residential and mobile IPs are safer, but only if they remain consistent per account.
When accounts jump between IPs or share IPs, clustering becomes easy for the algorithm to detect.
Browser and Device Fingerprinting
Twitter collects device fingerprints that include screen resolution, operating system, fonts, GPU details, time zone, language, and dozens of other signals. Two accounts logging in from different IPs but using identical browser fingerprints are still linked.
This is why using simple Chrome profiles or incognito windows is not enough. Without fingerprint isolation, Twitter can map entire networks together even when proxies are used.
Behavioral Pattern Analysis
The most powerful detection layer is behavioral. Twitter tracks how often accounts post, how quickly they reply, what time of day they are active, how often they like or retweet, and how long they remain idle between actions.
If 20 accounts reply within 90 seconds of a tweet going live, that is not enthusiasm. That is coordination. If the same accounts always engage with the same content, the system learns their relationships. Over time, Twitter builds probabilistic models of who is acting independently and who is acting as a group.
Social Graph Overlap
Finally, Twitter maps who follows whom, who replies to whom, and who appears in whose conversations. Networks that are too internally connected become visible. Real communities have overlap, but they also have randomness. Artificial networks are too neat.
The Three Rules of Undetectable Multi-Account Engagement
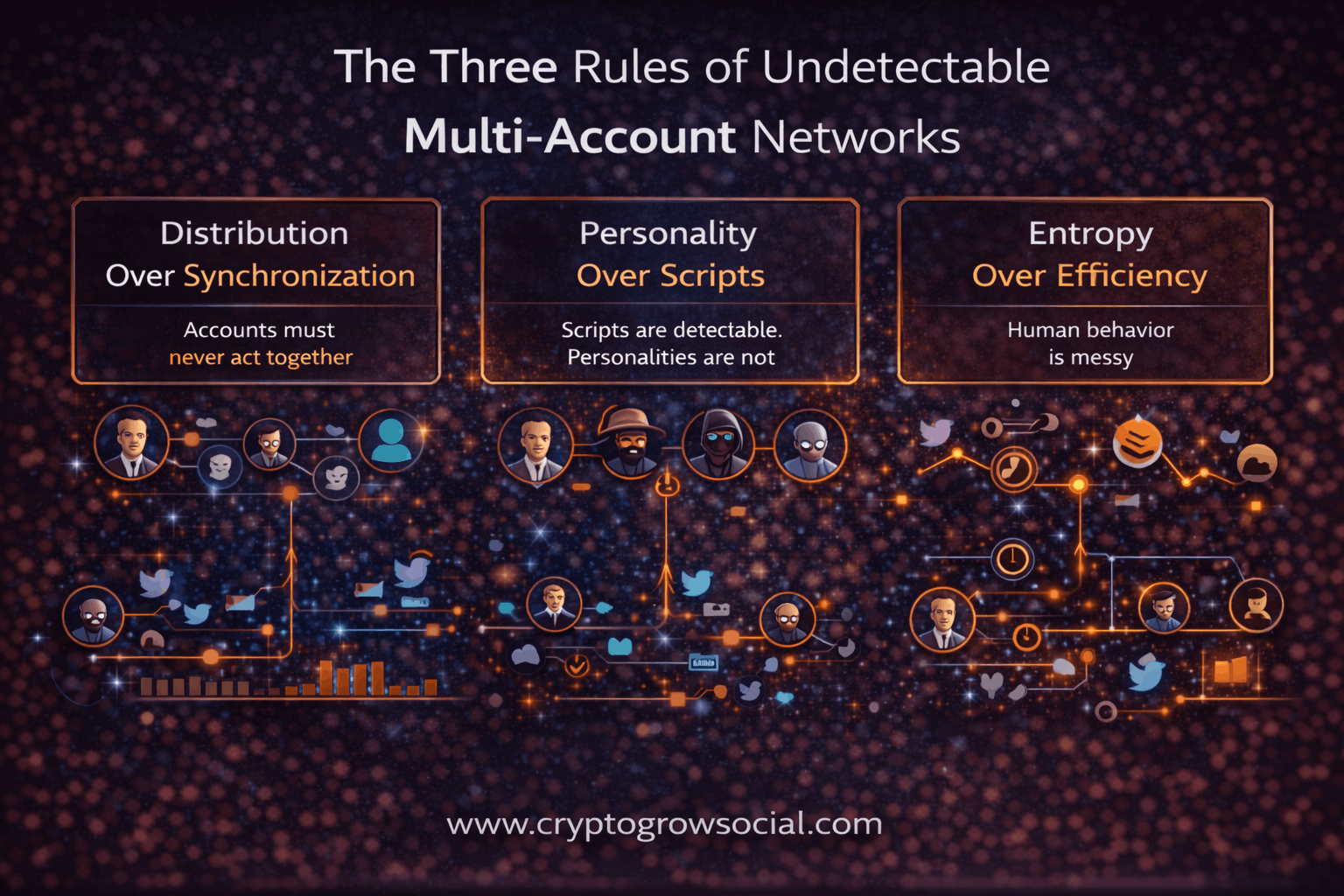
If you want a multi-account Crypto Twitter network to survive long term, you must design it for behavioral realism, not mechanical efficiency. X does not detect “bots.” It detects clusters of accounts that move, speak, and react too similarly. These three rules are what prevent that clustering.
Distribution Over Synchronization
Accounts must never act together.
When many accounts post, reply, or engage inside the same time window, the platform’s systems can mathematically link them into a cluster. Once that cluster exists, suppression or bans become inevitable.
A safe network spreads activity across hours and days. Some accounts respond quickly. Some much later. Some never engage at all. This creates statistical separation, which makes accounts look like independent people instead of a coordinated system.
Personality Over Scripts
Scripts are detectable. Personalities are not.
If multiple accounts use the same tone, structure, or phrasing, even with different words, machine learning systems can group them. Each account must feel like a different human with its own voice, interests, and emotional style.
Some should be analytical. Some sarcastic. Some emotional. Some casual. This diversity breaks linguistic and behavioral fingerprints that lead to detection.
Entropy Over Efficiency
Human behavior is messy, and your network must be messy too.
Some accounts should disappear for days. Some should post off-topic content. Some should forget to engage. This randomness prevents the network from becoming too clean, too predictable, and therefore too easy to detect.
A safe network does not try to be efficient. It tries to be believable.
Account Architecture That Prevents Clustering
A serious multi-account operation does not treat all accounts equally. Each account has a role inside a larger behavioral ecosystem.
Primary Voices
These are the accounts that post original threads, opinions, and narratives. They are the visible faces of the network. They must be the most carefully warmed, the most personality-driven, and the most human.
Secondary Amplifiers
These accounts reply, quote, and engage with primary voices. They should not always support them. Sometimes they should disagree, question, or reframe. This creates realism and avoids pattern formation.
Background Noise Accounts
These accounts exist to make the network feel alive. They post memes, comment on unrelated topics, talk about markets, sports, or life. Their purpose is to dilute the signal so that nothing looks coordinated.
How to Structure Engagement Without Triggering Detection?
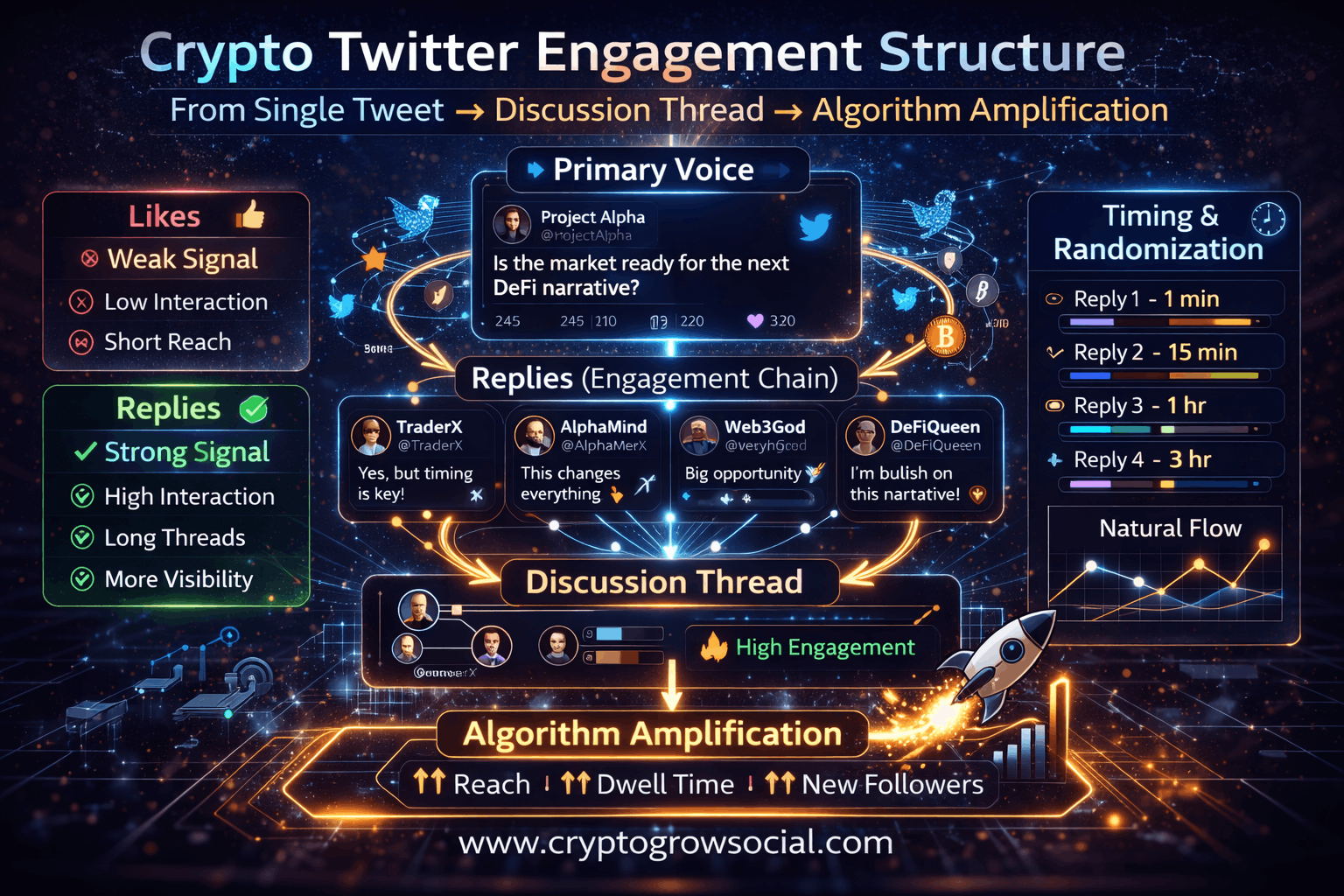
In modern Crypto Twitter operations, engagement is not measured by how many likes or replies a tweet receives, but by how effectively it pulls real people into a sustained conversation. The X algorithm is designed to prioritize content that creates reading time, scrolling depth, and interaction chains, not just surface-level signals. A tweet that gets one hundred likes and no replies is far less valuable than a tweet that generates ten back-and-forth discussions, because discussions force users to stop, read, and mentally participate.
This is why serious multi-account systems are built around engagement structure rather than engagement volume. The goal is not to make a tweet look popular. The goal is to make it look interesting. Interesting content causes humans to slow down. When humans slow down, the algorithm expands distribution.
When engagement is engineered correctly, the algorithm cannot distinguish between organic curiosity and synthetic coordination, because both produce the same behavioral footprint: people reading, replying, and thinking.
Why Replies Matter More Than Likes?
Likes are the weakest engagement signal on X. They are easy to give, easy to automate, and easy for the algorithm to discount. A like requires no cognitive effort and no time investment from the user. Because of this, likes do very little to increase reach.
Replies, by contrast, are extremely powerful because they force the reader to pause, process the content, and form a response. Every reply adds another line of text that other users can read, scroll through, and engage with. That increases dwell time, which is one of the most important ranking signals inside the Twitter algorithm.
From the platform’s perspective, a thread with ten thoughtful replies looks like a conversation that people care about. A tweet with one hundred likes looks like something people acknowledged and moved past. One creates distribution. The other does not.
This is why professional engagement networks are reply-first systems. Their purpose is to turn single tweets into conversation hubs. When several different accounts ask questions, challenge ideas, add context, or expand on a point, the tweet stops being content and becomes a discussion. Discussions are what the algorithm promotes.
For crypto projects, this is especially important because belief is created through discourse. Traders do not trust ads. They trust debates. They trust seeing multiple people argue about the same idea. Replies create that environment.
Why Quote Tweets Are Riskier Than Replies?
Quote tweets are double-edged weapons. On one hand, they can dramatically increase reach by reframing content into new timelines. On the other hand, they create extremely visible relationship data.
When the same group of accounts repeatedly quote the same primary account, Twitter can easily map that as a coordinated cluster. Quotes form strong social graph links. Replies, by contrast, are much more diffuse. People reply to many accounts, many topics, and many threads every day. That makes reply patterns harder to use for clustering.
For multi-account engagement, this means that quote tweets should be used sparingly and strategically. They are best reserved for accounts that already look independent and have their own audiences. Using too many quote tweets from the same network of accounts creates obvious reinforcement loops that are easy for detection systems to flag.
Replies are safer because they look like natural participation. A trader replying to a thread is normal. Ten traders replying over a few hours is also normal. Ten traders quote-tweeting the same post within minutes is not.
A professional network therefore leans heavily on replies for depth and uses quote tweets only when they can plausibly look independent.
Timing, Randomization, and Human Simulation
One of the most common mistakes in multi-account systems is treating time as a scheduling problem instead of a behavioral signal. Humans do not act on neat, evenly spaced schedules. They post when they wake up, when they are bored, when something catches their attention, or when they are procrastinating. Their activity clusters are messy and irregular.
To survive detection, a network must replicate this messiness.
Some accounts should post in the morning. Others should come alive at night. Some should disappear for days and then suddenly become active. Some should binge replies for an hour and then go silent. Some should engage heavily with crypto for a week and then talk about something else.
Time zones must vary. Sleep cycles must exist. Engagement bursts should appear spontaneous, not scheduled.
The purpose of this randomness is not to confuse humans. It is to prevent machine learning systems from finding clean statistical patterns. Algorithms are extremely good at detecting uniformity. They are very bad at detecting controlled chaos.
The more human your timing looks, the less detectable your network becomes.
Narrative-First Engagement Strategy
The biggest strategic error crypto teams make with multi-account engagement is pushing their project too early. When accounts immediately start mentioning a token, a protocol, or a brand, they turn themselves into advertisers. Advertisers get ignored by both humans and algorithms.
The correct approach is narrative-first.
First, the network discusses the problem. Accounts talk about what is broken in the market, what traders are frustrated with, or what builders are struggling to solve.
Then the network discusses trends. It explores where the market seems to be going, what new approaches are emerging, and why old models are starting to fail.
Then the network discusses why existing solutions are insufficient.
Only after this context exists does the project appear, not as a promotion, but as a natural conclusion of the discussion.
When this sequence is followed, the project does not look like marketing. It looks like the answer to a question the market has already been asking. When multiple accounts repeat the same idea across different threads, people begin to internalize it. They start repeating it themselves. That is how belief is formed.
And in crypto, belief is what moves liquidity.
Common Mistakes That Kill Multi-Account Networks
Most crypto Twitter farms do not collapse because automation does not work. They collapse because they create patterns that the X algorithm can easily identify. Twitter does not ban bots; it suppresses clusters of accounts that behave too similarly, too predictably, or too aggressively. When a network starts to look coordinated instead of organic, its distribution power disappears almost overnight.
Understanding these failure points is critical, because even expensive infrastructure becomes useless if the behavioral layer is wrong.
Mirror Posting and Text Reuse
One of the fastest ways to expose a network is when multiple accounts post the same or nearly identical content. Even small variations in wording are often not enough, because Twitter analyzes semantic similarity, not just exact text matches.
When ten accounts post versions of the same tweet within a short time window, the system treats them as a coordinated unit. Once that happens, all of those accounts begin sharing the same distribution fate. If one is suppressed, the rest usually follow.
A real network must speak with many voices, not one script.
Synchronized Replies and Engagement Waves
Another fatal mistake is timing coordination. When a primary account posts and ten other accounts reply within two minutes, the pattern is obvious. Real people do not behave like that. They notice posts at different times, scroll at different speeds, and react when they feel like it.
Professional networks spread engagement across hours, not minutes. Some accounts might reply quickly. Others might show up much later. This creates a natural engagement curve that looks organic instead of manufactured.
Uniform speed is one of the strongest signals of automation.
Centralized IP and Infrastructure Footprints
Running many accounts from the same IP ranges, data center blocks, or browser environments creates clustering. Even if the content looks natural, shared infrastructure links accounts together.
When Twitter identifies that cluster, everything inside it becomes vulnerable. A single flagged account can poison dozens of others.
This is why serious farms use residential or mobile IPs, persistent geolocation, and isolated browser fingerprints for every account. Infrastructure separation is not optional. It is the foundation of survival.
Manual Logins from Home or Office Networks
Many teams destroy their own farms by logging into bot accounts from their personal IPs. The moment a single home or office connection touches dozens of accounts, Twitter can link them instantly.
From that point on, even perfectly behaved accounts are treated as a coordinated operation.
A professional network is never accessed directly from human networks. All access happens through controlled environments that preserve separation.
Over-Promotion and Narrative Short-Circuiting
Even when the technical side is perfect, content can still kill a network.
If accounts constantly mention the same project, drop links, or shill tokens, they look like advertisers. Advertisers do not generate discussion, and discussion is what drives distribution.
The correct strategy is narrative-first. Accounts should mostly talk about the market, trends, problems, and ideas. Your project should appear only when it naturally fits that story.
Restraint creates credibility. Credibility creates reach.
How Professional Crypto Teams Run Engagement Networks?
Professional crypto teams do not approach Twitter as a place to “post content.” They approach it as a market where attention is traded, accumulated, and deployed. Every serious project that dominates Crypto Twitter operates on two separate layers: infrastructure and narrative. One provides reach. The other gives that reach something meaningful to carry.
What separates elite teams from amateurs is not budget, but architecture.
Infrastructure Is Treated as a Distribution Layer
Top teams never rely on a single Twitter account, no matter how many followers it has. They understand that one account is a single point of failure. If it is shadowbanned, ignored, or algorithmically deprioritized, the entire project disappears.
Instead, they operate networks of distributed identities. These accounts live in different niches of Crypto Twitter: traders, builders, NFT communities, meme culture, macro discussions, and alpha circles. Each one has its own history, personality, and follower graph.
To the algorithm, this looks like the market itself talking. To users, it feels like a project is naturally everywhere.
That is real distribution.
Narrative Is Engineered Before Promotion Ever Begins
Elite teams never ask, “How do we promote our token?”
They ask, “What does the market need to believe for our token to feel inevitable?”
Before a single account mentions a project, the network begins shaping the surrounding conversation. Some accounts discuss why a sector is broken. Others debate new trends. Others criticize incumbents. Over time, a shared mental frame forms inside Crypto Twitter.
When the project finally appears, it does not feel like marketing. It feels like the answer the market has already been looking for.
This is how narratives become self-reinforcing.
Distributed Identities Replace Influencer Dependency
Most amateur teams try to buy influence. They pay one or two large accounts to tweet about them and hope that works.
Professional teams do the opposite. They create influence.
By operating dozens or hundreds of medium-sized, believable accounts, they no longer need any single influencer. Their own network produces enough conversation to trigger algorithmic amplification and social proof.
Influencers then begin responding to the network, not the other way around.
That is when a project moves from being advertised to being discussed.
No Single Account Is Allowed to Carry the Story
One of the most important rules inside elite engagement networks is that no account is special. Founder accounts, project accounts, and network accounts all play different roles, but none of them are allowed to become the only source of truth.
- If the founder stops posting, the network keeps the narrative alive.
- If the main account is throttled, other accounts continue pushing the story.
- If a single voice disappears, the market still hears the same message.
This redundancy is what makes large crypto narratives unstoppable.
Engagement Is Designed to Create Market Signals, Not Vanity Metrics
Professional teams do not chase likes or retweets. They watch for:
- Accounts they do not control referencing their narrative
- Traders asking questions
- Influencers replying
- Communities repeating the story
Those are the signals that a narrative has escaped the network and entered the market.
Once that happens, attention compounds on its own.
How CryptoGrowSocial Solves This at Scale?
As crypto teams begin to understand how professional engagement networks actually operate, they quickly run into a brutal reality: the technical and operational burden of running this infrastructure internally is far larger than it appears on paper. Managing even fifty accounts safely requires residential or mobile proxies, browser fingerprinting, automation layers, warm-up workflows, content pipelines, monitoring dashboards, and continuous human oversight. When that number grows into the hundreds, the operation stops being a growth function and becomes an engineering department.
This is precisely the gap CryptoGrowSocial was built to fill. It exists for founders, token teams, and Web3 startups that need market-level narrative distribution but do not want to become infrastructure companies just to survive on Crypto Twitter. Instead of forcing teams to build fragile farms, CryptoGrowSocial provides production-grade distribution systems that already work inside the real attention economy.
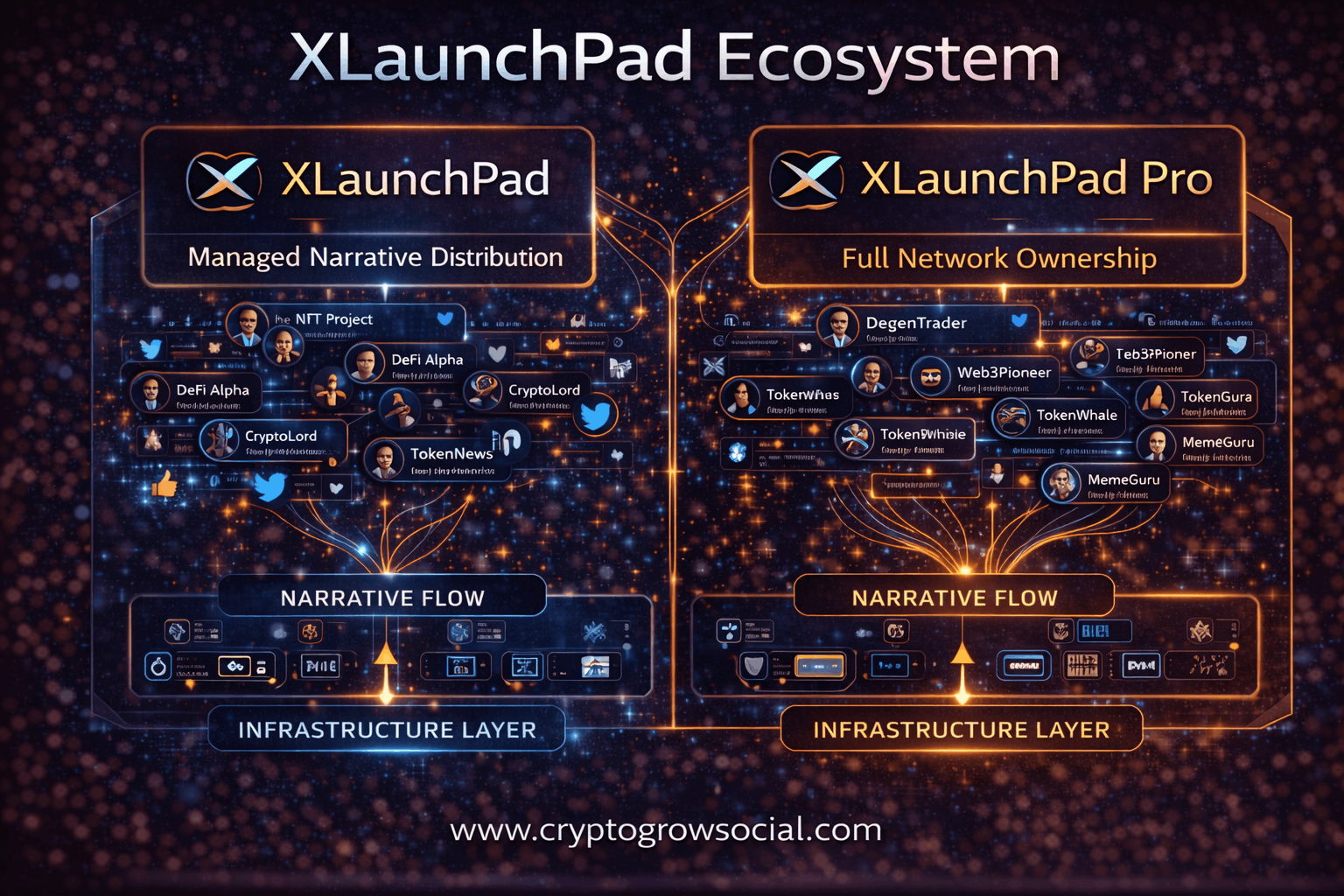
XLaunchPad — Managed Narrative Distribution
XLaunchPad is designed for teams that need immediate reach without taking on technical risk. Instead of handing you software, servers, or accounts, it connects your project directly into a live, aged, professionally operated crypto Twitter network that already exists inside trader circles, influencer threads, and market debates.
- You do not receive bots.
- You do not log into accounts.
- You do not configure proxies or fingerprints.
What you provide is your narrative: your positioning, your story, and the ideas you want the market to internalize. The network then places that narrative into real conversations that already have liquidity of attention. This means your project does not have to fight for visibility from zero. It enters where people are already reading, replying, and forming opinions.
Because the accounts are aged, socially embedded, and behaviorally diverse, the activity does not look like promotion. It looks like organic market discourse. That is what allows projects using XLaunchPad to appear everywhere that matters without exposing themselves to bans, shadow suppression, or the operational chaos that normally comes with running large account networks.
XLaunchPad Pro — Full Network Ownership
XLaunchPad Pro is built for teams that want control rather than access. Instead of plugging into a shared network, you receive a dedicated, professionally constructed Twitter distribution system that is fully yours.
This includes aged and warmed accounts, residential and mobile proxy routing, fingerprint isolation, automation frameworks, narrative coordination tools, and engagement logic that has already been tested under real market conditions. Instead of spending months hiring engineers, buying software, trial-and-error warming accounts, and rebuilding after bans, you start with a system that is already stable.
From day one, your team can deploy narratives, seed discussions, defend market perception, and scale engagement across dozens or hundreds of accounts without touching the underlying infrastructure. The technology becomes invisible, allowing your focus to stay on what actually matters: controlling how the market thinks about your project.
In practice, this gives teams the same strategic advantage that only large, well-funded crypto organizations normally have, but without the time, cost, and fragility of building everything from scratch.
Build vs Rent: Which Makes Sense for Your Project
Every crypto team eventually faces the same decision: do you build your own Twitter engagement network, or do you plug into one that already exists? Both paths can work in theory, but they lead to very different risk profiles, timelines, and capital requirements. The right choice is not about ideology or control, but about what your team can realistically execute without destroying momentum.
Below is a clear breakdown of what each path actually involves in 2026.
Building Your Own Crypto Twitter Network
Building your own network means you own everything: the accounts, the infrastructure, the automation, and the narrative flow. In theory, this gives you maximum control and long-term leverage. In practice, it turns your marketing team into an infrastructure company.
To build a functional network, you must acquire or create aged accounts, warm them for weeks, assign unique residential or mobile IPs, isolate fingerprints, and run automation that never produces detectable patterns. This is not a one-time setup. Accounts constantly die, IPs get flagged, fingerprints leak, and Twitter updates its detection models. Maintenance never stops.
The advantage of building is that you are not dependent on any external provider. You can deploy narratives whenever you want, at any scale, and you are not paying placement fees per campaign. For large, well-funded teams with in-house engineers and long timelines, this can eventually become a strategic asset.
The downside is risk and burn rate. Most DIY farms collapse because one layer fails: proxies get correlated, automation synchronizes, or accounts get clustered. When that happens, entire networks disappear. Months of warming and thousands of dollars in accounts can vanish in days. While you are fighting infrastructure fires, your competitors are capturing attention.
Building only makes sense if you can afford to lose money, time, and accounts while learning how not to get detected.
Renting or Owning Through a Professional Network
Renting or owning through a professional system like CryptoGrowSocial means you skip the entire infrastructure phase. You do not deal with account creation, warming, proxies, fingerprints, or automation logic. You start with a network that already exists inside Crypto Twitter and already behaves like real people.
The main advantage is speed and reliability. You can inject narratives into trader threads, influencer replies, and market discussions immediately, without waiting 30 to 60 days for accounts to mature. The technical risk is carried by the provider, not by your team.
There is also a strategic benefit. Because the infrastructure is stable, you can focus on messaging, positioning, and timing instead of debugging systems. This almost always leads to stronger narratives and faster market response, which is what actually moves charts.
The trade-off is that you are paying for expertise, stability, and reach rather than building everything yourself. However, for most crypto teams, this is not a weakness. It is the reason they survive long enough to matter.
In an attention-driven market, the teams that win are the ones that can deploy distribution safely and immediately. For almost everyone outside of large, engineering-heavy organizations, renting or owning a professional network is not just easier — it is the rational choice.
Conclusion
Crypto Twitter is no longer about who posts the best threads. It is about who controls the conversation at scale. Multi-account engagement, when done correctly, turns a single idea into a market-wide narrative. When done poorly, it turns a project invisible.
Whether you choose managed distribution through XLaunchPad or full ownership through XLaunchPad Pro, CryptoGrowSocial gives you what most teams will never successfully build on their own: a real, undetectable attention network inside the crypto economy.